Documentation
Introduction
- Overview
- Getting Started
- Support for K8s Installers
- Deploying on Kind
- Deploying on Minikube
- Configuration
- Installing with Helm
Cloud Deployment
Reference
- Antrea Network Policy
- Antctl
- Architecture
- Traffic Encryption (Ipsec / WireGuard)
- Securing Control Plane
- Security considerations
- Troubleshooting
- OS-specific Known Issues
- OVS Pipeline
- Feature Gates
- Antrea Proxy
- Network Flow Visibility
- Traceflow Guide
- NoEncap and Hybrid Traffic Modes
- Egress Guide
- NodePortLocal Guide
- Antrea IPAM Guide
- Exposing Services of type LoadBalancer
- Traffic Control
- Versioning
- Antrea API Groups
- Antrea API Reference
Windows
Integrations
Cookbooks
Multicluster
Developer Guide
Project Information
Antrea


Overview
Antrea is a Kubernetes networking solution intended to be Kubernetes native. It operates at Layer 3/4 to provide networking and security services for a Kubernetes cluster, leveraging
Open vSwitch as the networking data plane.
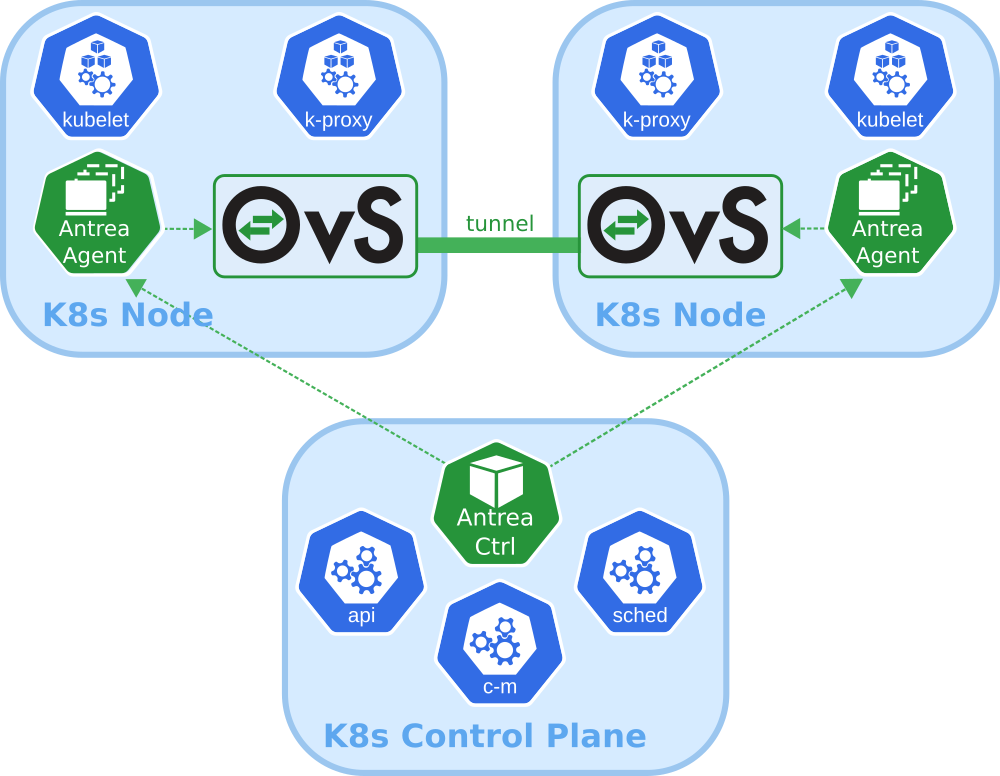
Open vSwitch is a widely adopted high-performance programmable virtual switch; Antrea leverages it to implement Pod networking and security features. For instance, Open vSwitch enables Antrea to implement Kubernetes Network Policies in a very efficient manner.
Prerequisites
Antrea has been tested with Kubernetes clusters running version 1.16 or later.
NodeIPAMControllermust be enabled in the Kubernetes cluster.
When deploying a cluster with kubeadm the--pod-network-cidr <cidr>option must be specified. Alternately, NodeIPAM feature of Antrea Controller should be enabled and configured.- Open vSwitch kernel module must be present on every Kubernetes node.
Getting Started
Getting started with Antrea is very simple, and takes only a few minutes. See how it’s done in the Getting started document.
Contributing
The Antrea community welcomes new contributors. We are waiting for your PRs!
- Before contributing, please get familiar with our
- Check out the Antrea Contributor Guide for information about setting up your development environment and our contribution workflow.
- Learn about Antrea’s Architecture and Design. Your feedback is more than welcome!
- Check out Open Issues.
- Join the Antrea community and ask us any question you may have.
Community
- Join the
Kubernetes Slack and look for our
#antrea channel.
- Check the
Antrea Team Calendar
and join the developer and user communities!
- The Antrea community meeting, every two weeks on Tuesday at 5AM GMT+1 (United Kingdom time). See Antrea team calendar for localized times.
- Antrea live office hours, every two weeks on Tuesday at 10PM GMT+1 (United Kingdom time). See Antrea team calendar for localized times.
- Join our mailing lists to always stay up-to-date with Antrea development:
- projectantrea-announce for important project announcements.
- projectantrea for updates about Antrea or provide feedback.
- projectantrea-dev to participate in discussions on Antrea development.
Also check out @ProjectAntrea on Twitter!
Features
- Kubernetes-native: Antrea follows best practices to extend the Kubernetes APIs and provide familiar abstractions to users, while also leveraging Kubernetes libraries in its own implementation.
- Powered by Open vSwitch: Antrea relies on Open vSwitch to implement all networking functions, including Kubernetes Service load-balancing, and to enable hardware offloading in order to support the most demanding workloads.
- Run everywhere: Run Antrea in private clouds, public clouds and on bare metal, and select the appropriate traffic mode (with or without overlay) based on your infrastructure and use case.
- Comprehensive policy model: Antrea provides a comprehensive network policy model, which builds upon Kubernetes Network Policies with new features such as policy tiering, rule priorities and cluster-level policies.
- Windows Node support: Thanks to the portability of Open vSwitch, Antrea can use the same data plane implementation on both Linux and Windows Kubernetes Nodes.
- Troubleshooting and monitoring tools: Antrea comes with CLI and UI tools which provide visibility and diagnostics capabilities (packet tracing, policy analysis, flow inspection). It exposes Prometheus metrics and supports exporting network flow information to collectors and analyzers.
- Network observability and analytics: Antrea + Theia enable fine-grained visibility into the communication among Kubernetes workloads. Theia provides visualization for Antrea network flows in Grafana dashboards, and recommends Network Policies to secure the workloads.
- Network Policies for virtual machines: Antrea native policies can be
enforced on non-Kubernetes Nodes including VMs and baremetal servers. Project
Nephe implements security policies for VMs across clouds, leveraging Antrea native policies.
- Encryption: Encryption of inter-Node Pod traffic with IPsec or WireGuard tunnels.
- Easy deployment: Antrea is deployed by applying a single YAML manifest file.
To explore more Antrea features and their usage, check the Getting started document and user guides in the Antrea documentation folder. Refer to the Changelogs for a detailed list of features introduced for each version release.
Adopters
For a list of Antrea Adopters, please refer to ADOPTERS.md.
Roadmap
We are adding features very quickly to Antrea. Check out the list of features we are considering on our Roadmap page. Feel free to throw your ideas in!
License
Antrea is licensed under the Apache License, version 2.0
